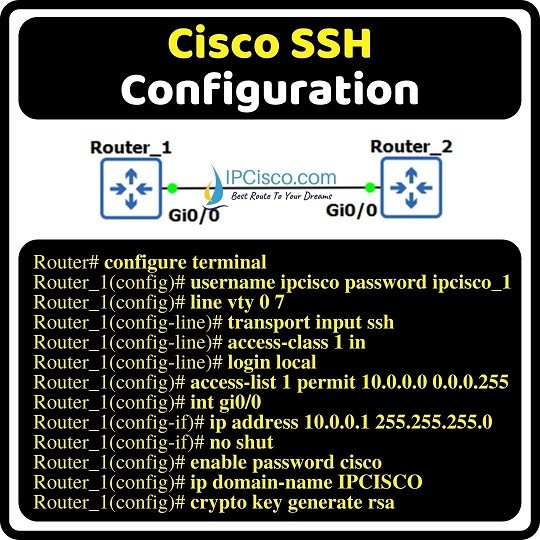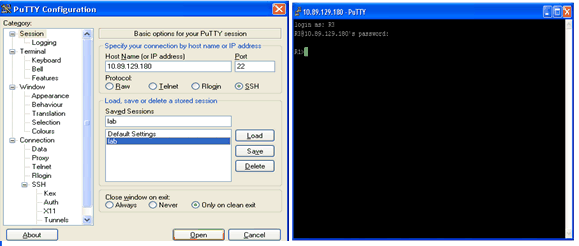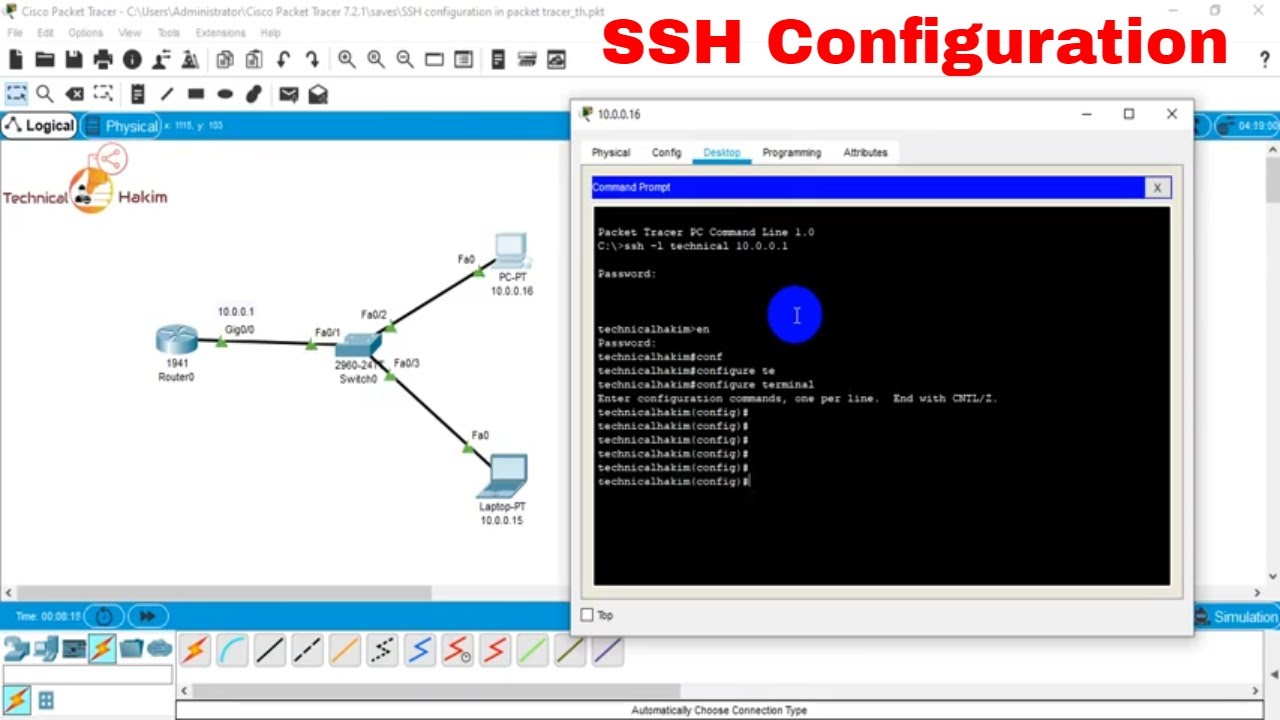
SSH configuration in cisco packet tracer | Technical Hakim #SSHconfigurationInPacketTracer - YouTube
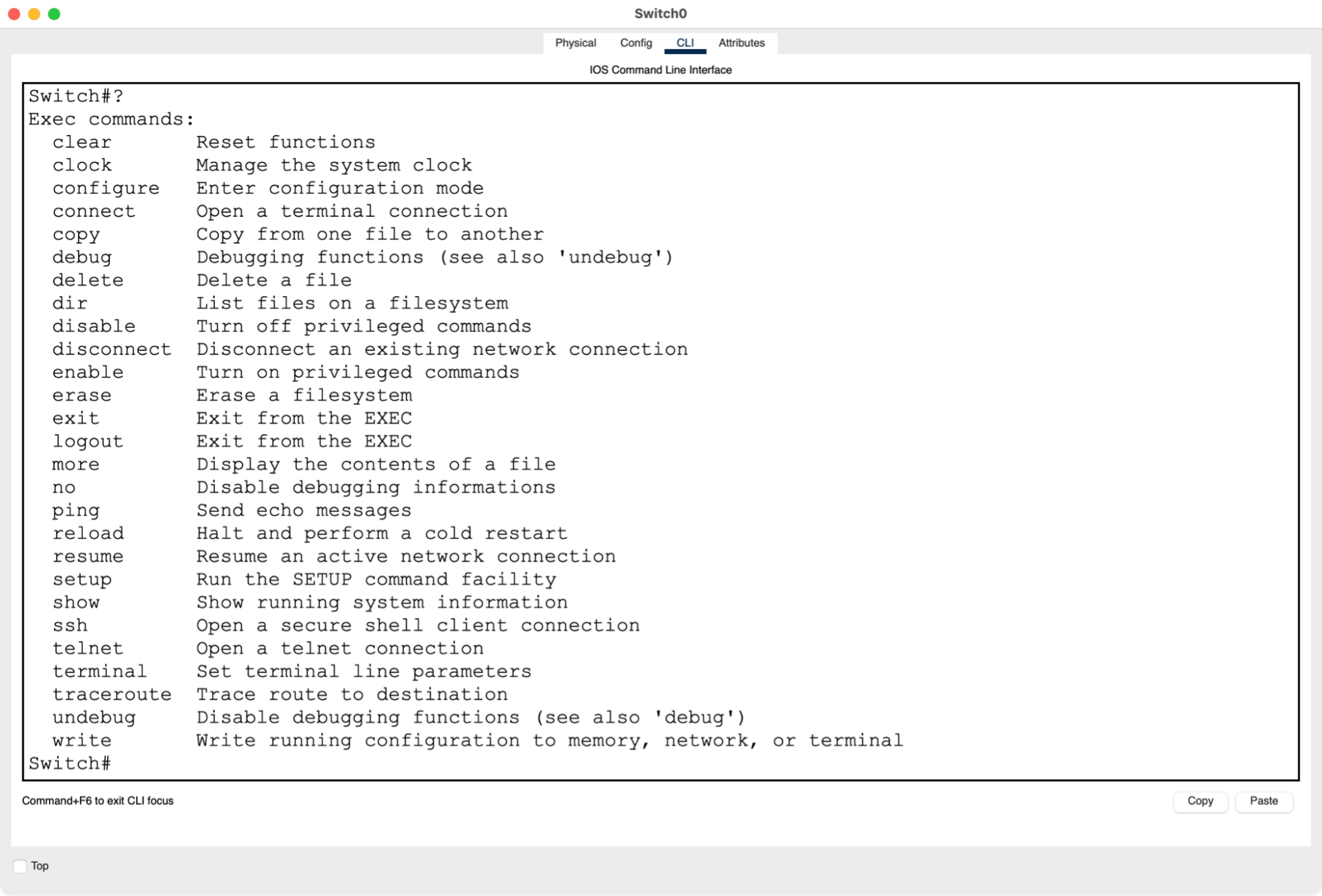
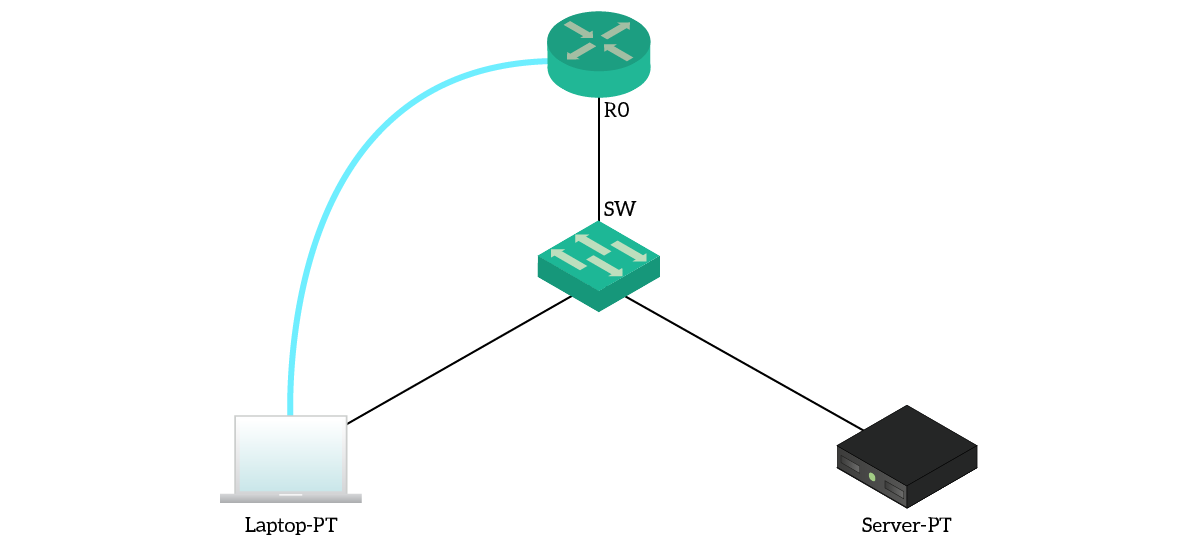
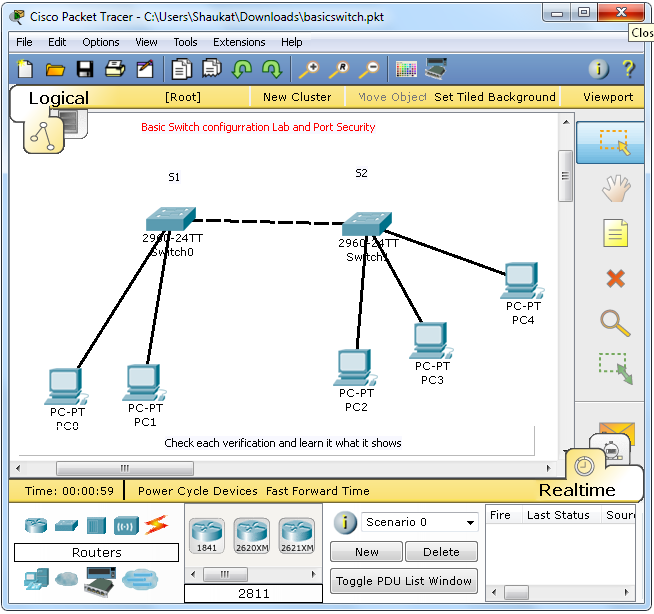
Understand the Command Line Interface (CLI) - Simulate Your Network Diagram With Cisco Packet Tracer - OpenClassrooms

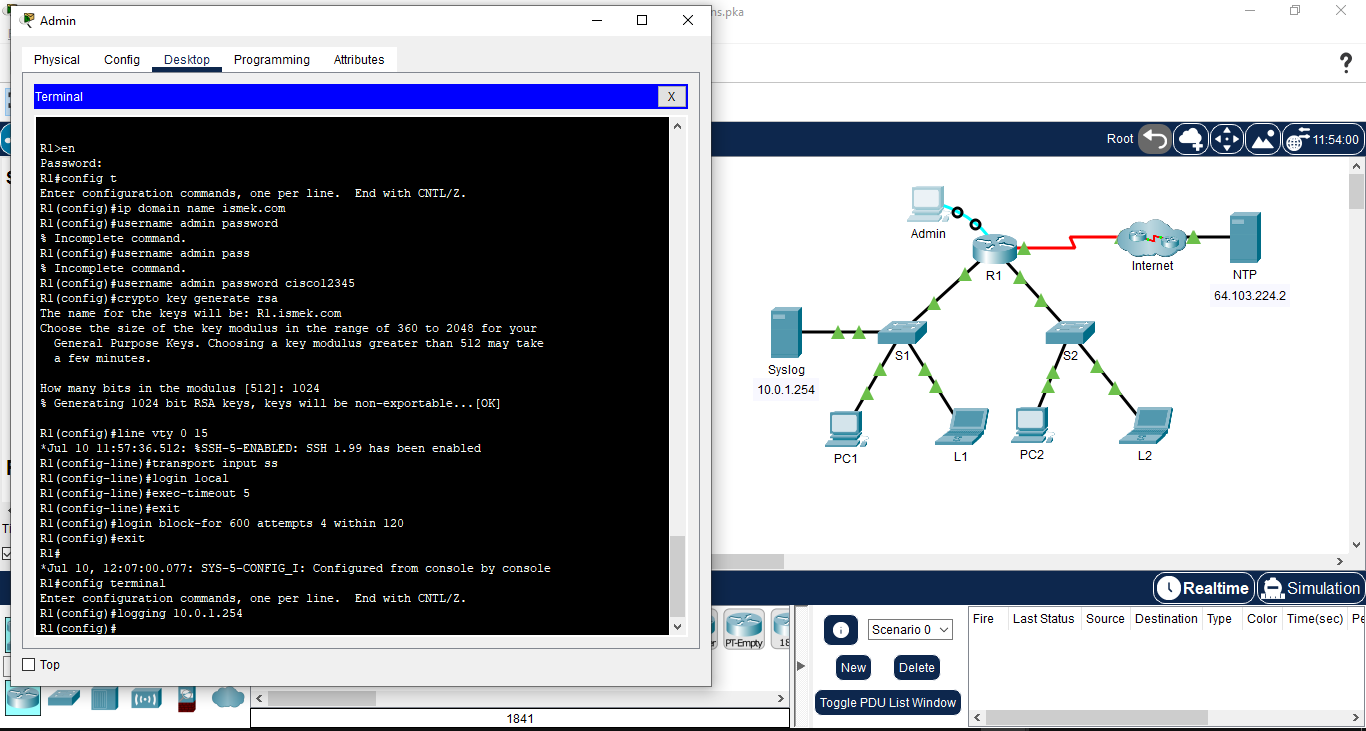
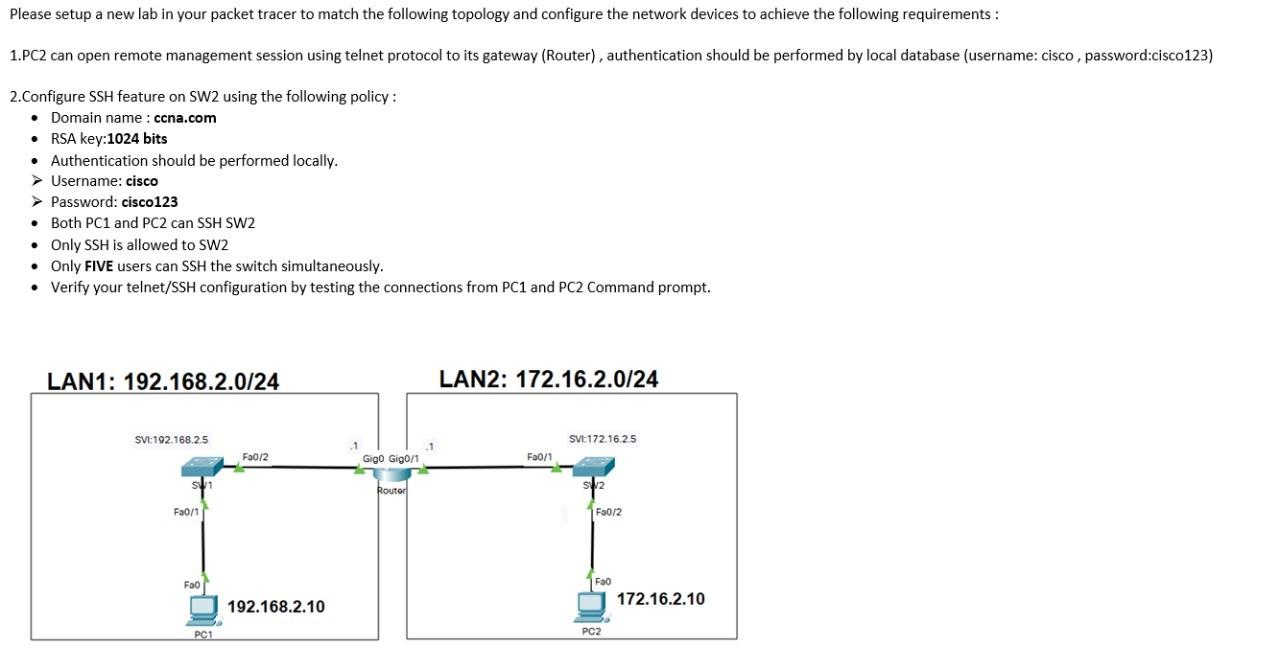
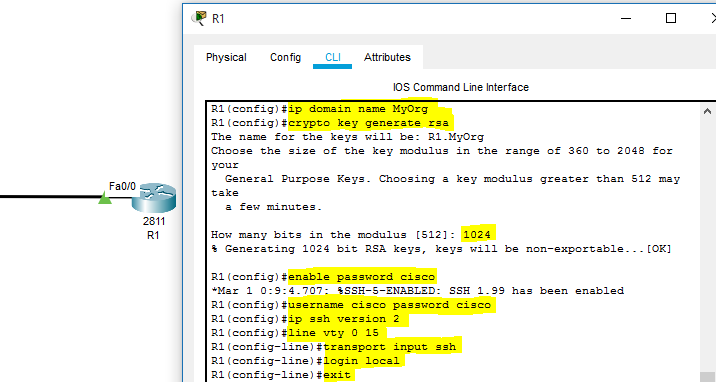
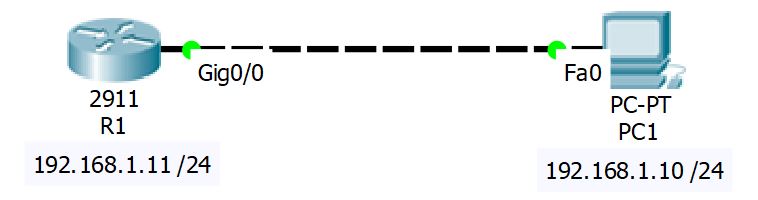
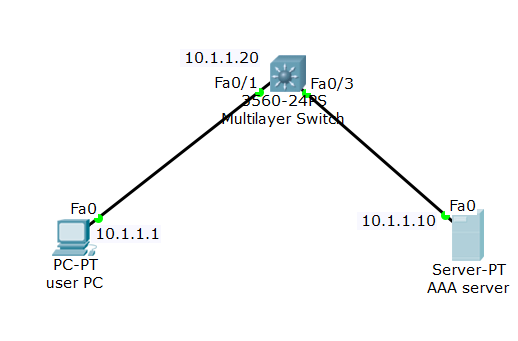
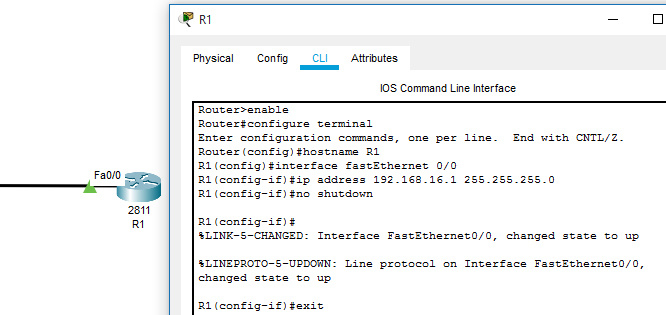
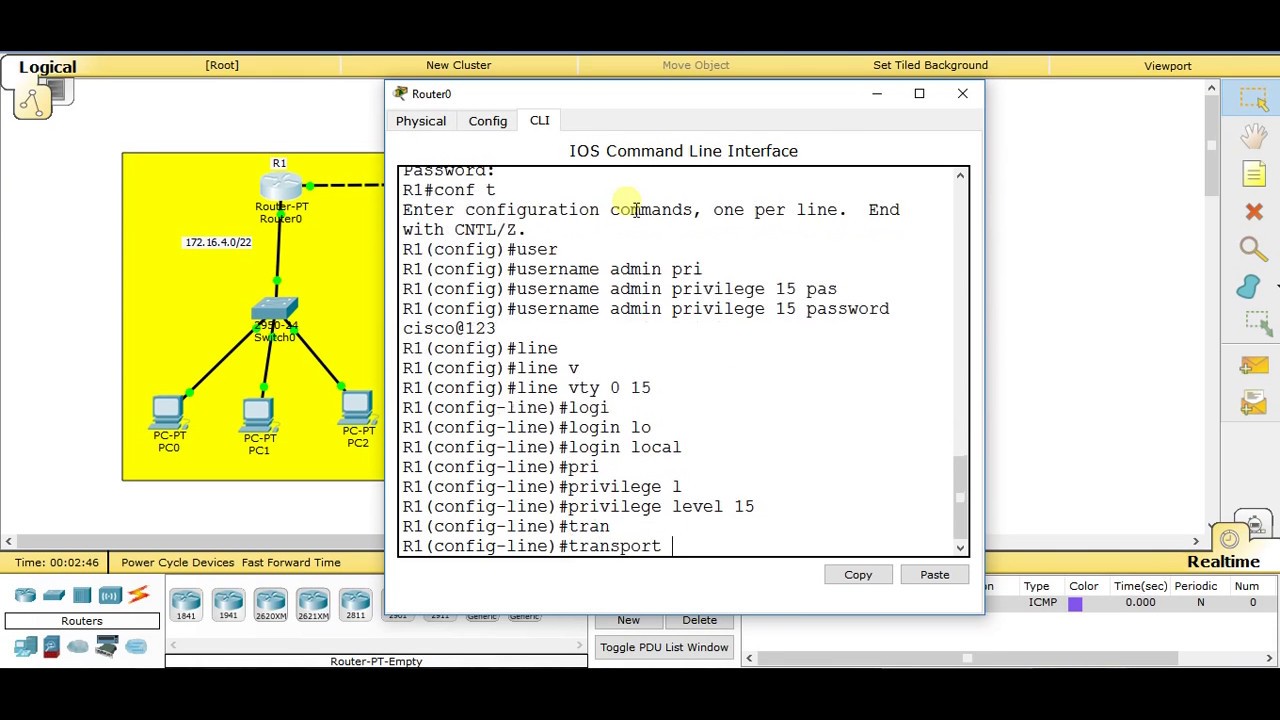
SSH CONFIGURATION ON CISCO ROUTER CCNA-LAB – Learn Linux CCNA CCNP CEH CISSP CISA Penetration-Testing Bug Bounty IPv6 Cyber-Security Network-Security Online
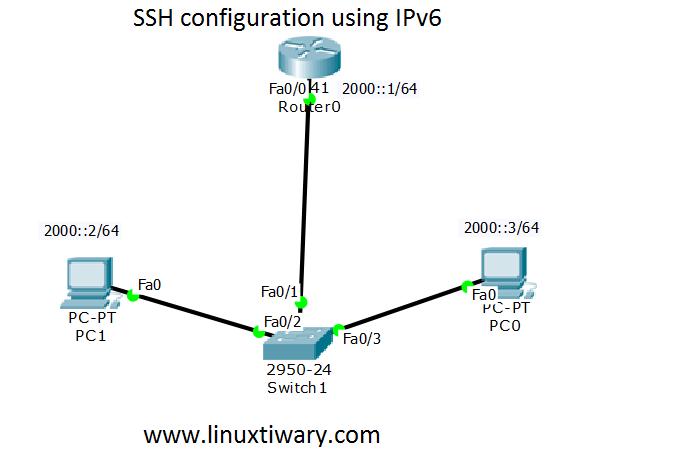
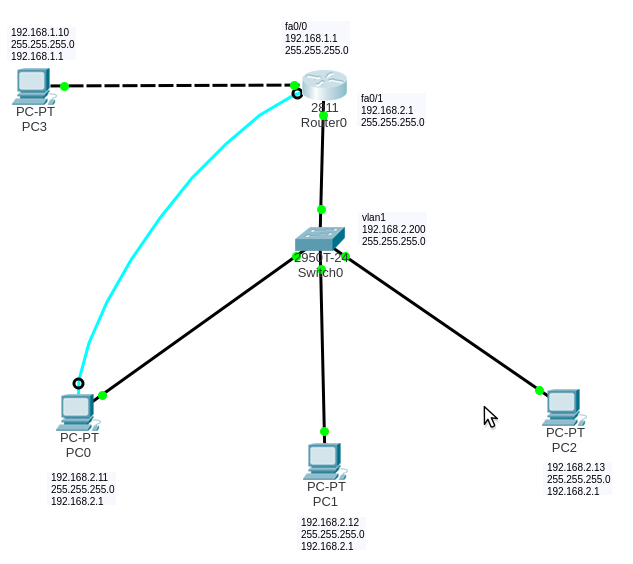
ssh configuration on cisco router using IPv6 – Learn Linux CCNA CCNP CEH CISSP CISA Penetration-Testing Bug Bounty IPv6 Cyber-Security Network-Security Online