Industry's First Microcontroller Integrated with a Robust Secure Subsystem and Arm® TrustZone® Technology | Elektor Magazine

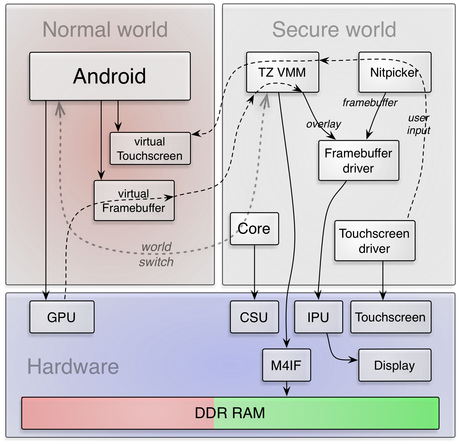
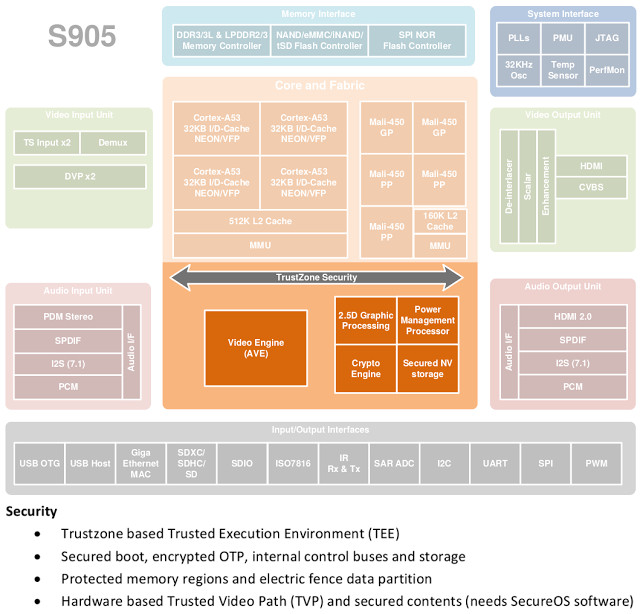
Self-secured devices: High performance and secure I/O access in TrustZone-based systems - ScienceDirect

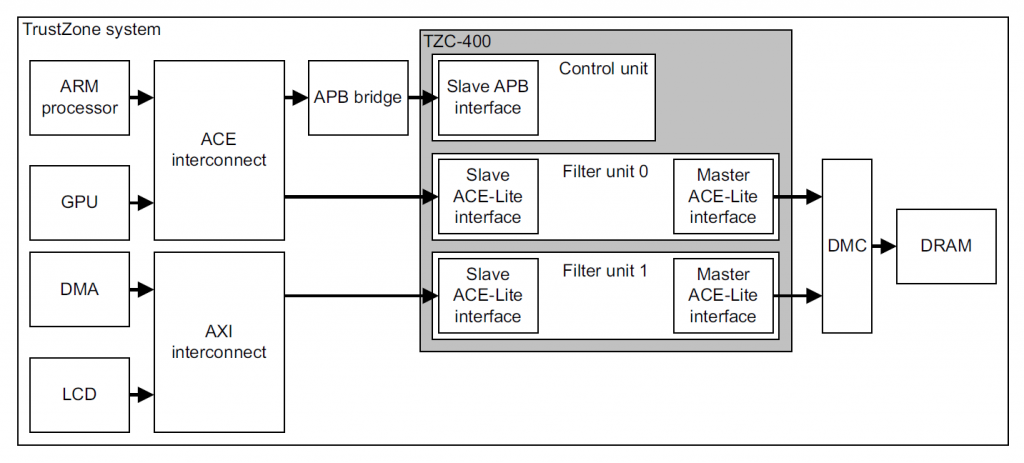
Attacking TrustZone on devices lacking memory protection | Journal of Computer Virology and Hacking Techniques
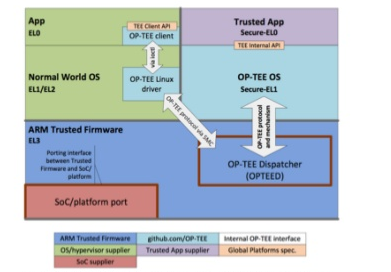
ARM Security Solutions and Intel Authenticated Flash -- How to integrate Intel Authenticated Flash with ARM TrustZone for maximum system protection

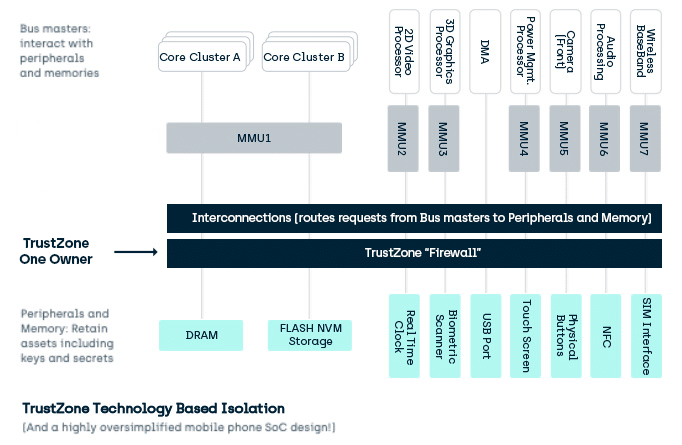
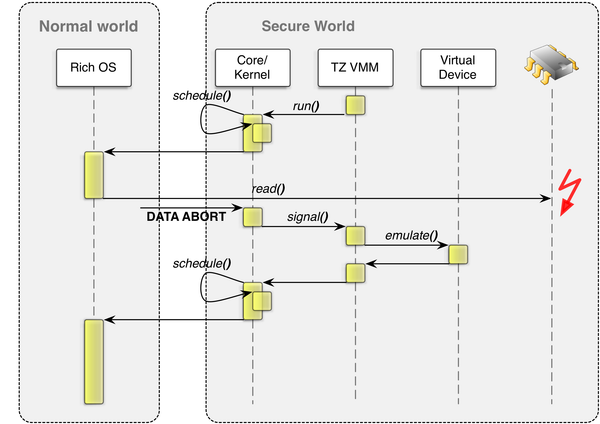
Attacking TrustZone on devices lacking memory protection | Journal of Computer Virology and Hacking Techniques
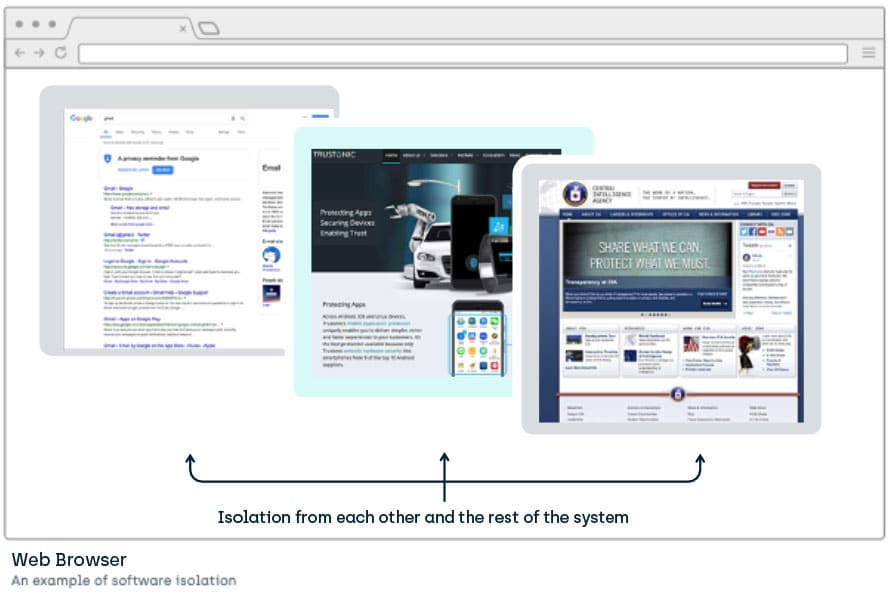
![System example partitioning secure and non-secure area with TrustZone [2]. | Download Scientific Diagram System example partitioning secure and non-secure area with TrustZone [2]. | Download Scientific Diagram](https://www.researchgate.net/publication/4278172/figure/fig1/AS:669986985091101@1536748753954/System-example-partitioning-secure-and-non-secure-area-with-TrustZone-2.png)